Penetration testing is used to evaluate the security of a computer system or network which is suffering from external attacks and malicious insiders. We use the active analytics program for any possible vulnerability in this process. You can visit https://www.radiusits.com/boston-it-support/vulnerability-assessments/ to know more about penetration test in Boston.
Penetration testing is valuable for the following reasons:
1. It determines the feasibility of a particular set of attack vectors.
2. Identify vulnerabilities from higher to lower order.
3. It identifies the vulnerabilities that are not detected by automated network or scanning software.
4. It provides evidence to support increased investment in personal safety and technology.
Penetration testing is a component of the security audit. It has several ways to do testing like black box testing and white box testing.
Black box testing is necessary for the tester to first determine the location and then extend the system to start their analysis.
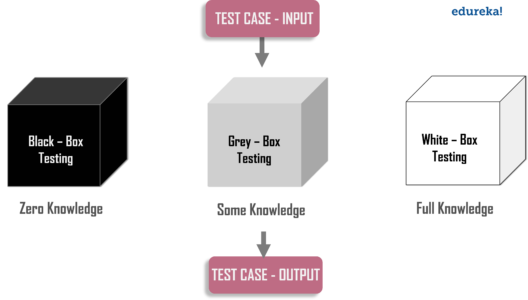
Image Source: Google
White box testing provides complete information about the infrastructure that will be tested and sometimes also provide network diagrams, source code and IP addressing information.
There is some variation between black and white box testing is known as gray box testing. Black box testing, white box testing and gray box testing, also known as the blind, full disclosure and appropriate testing of partial disclosure.
Penetration testing should be performed on each computer that will be used in a hostile environment, on a site overlooking the Internet, before the system is used.
Evaluation Of Penetration Testing In Security
